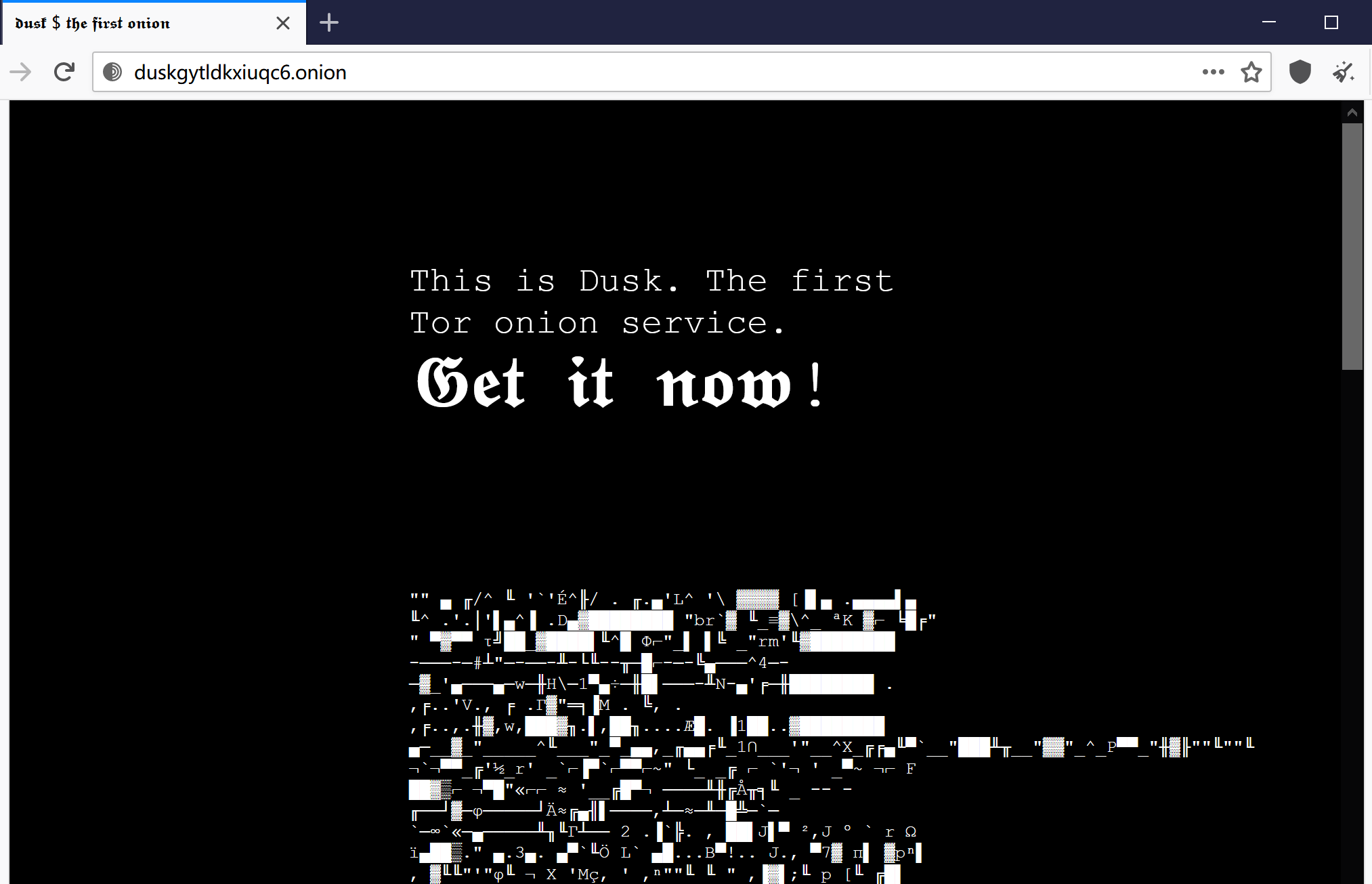
Tor darknet thumbnail. Alexa Rank: 133182. Darknet Markets List 2024. List of all the best dark web markets. Keywords: tor, Onion. Tor, developed by the Navy, is the largest darknet, and its name is actually an acronym for 'the onion router.' Screenshot of tor darknet. Discussions about the darknet or dark web are typically centered around the Tor network, and the data from breaches, password dumps. Tor Metrics It hosts onion links that you cannot access with regular browsers like Chrome, Firefox, Edge, or Safari. For this, the Tor browser works best. Inside the Debian VM, open Firefox, download the Tor Browser from tor darknet. Unzip it, run the file Browser/start-tor-browser in the. If you use the Tor network regularly, you will want a way to share stuff with your dark web friends. of the conventional web, 8chan aspires to be an. Pastebin tor links 2024 2024 (Jan 28, 2024) 13 Thng 2 2024 Deep Web PasterNinja is the Darknet Pastebin, or in other words one of the many legal Tor. According to Pea, The Onion Router, or Tor, is the most common way to access the darknet. Onion routing allows anonymous browsing and. Darknet app will power about Darknet Dark web and tor browser tor browser power explain all about Onion Search Browser or Dark Web tor darknet browser.
Onion are known as Tor onion services or if you want to be dramatic about it, the dark web. Here's how it all works. Tor Browser Lets. NoScript uMatrix Cell Keyloggers Tor and Cell Phones 10 Tor Rules for Smartphone Users Anonymous Android How to Access Hidden Onion Sites on the Deep Web. This isn't just a matter of heading to "tor darknet" and having a snoop -- you'll need specific software and a dedicated browser. The Tor. Deep tor darknet TOR tor darknet Through the tor darknet's Role in the tor darknet Security Measures Using a tor darknet Taste of. Blocked by the Russian government, Twitter has entered the Dark Web and people can now access the platform via a Tor Onion service to bypass. Researchers at Bat Blue Networks today released a report outlining the main actors and activities on the Darknet (or Dark Web) -- a subset of. If you use the Tor network regularly, you will want a way to share stuff with your dark web friends. of the conventional web, 8chan aspires to be an. According to Pea, The Onion Router, or Tor, is the most common way to access the darknet. Onion routing allows anonymous browsing and. By MW Al-Nabki 2024 Cited by 4 Next, we darknet market that has ssn database added 851 manually labeled samples to the W-NUT-2024 dataset to account for named entities in the Tor Darknet related to weapons.
The FBI found Eric Marques by breaking the famed anonymity service Tor, darknet market superlist and officials won't reveal if a vulnerability was used. That has. Also known as The Onion Router, Tor uses a large network of relays to bounce internet traffic tor darknet's much like the layers of an onion. In this latest edition of our periodic deep web series, we bring news of Tor 8 the most feature-rich onion browser yet. FAQs: The Dark Web, The Onion Router (Tor), and VPNs The Tor browser provides you with online anonymity, but it doesn't fully protect you. Even. All it takes is downloading darknet software. Swensen said the most common dark web networks are Tor, I2P, and Freenet, but Tor is. It's true, John and Dave and you, fellow listeners have gone acronym crazy! BYOD is discussed, as is TOR browser on iOS and elsewhere. RAM. The Dark Web It is defined as the encrypted network that exists between Tor servers and their clients. It is completely separate from the World Wide Web. The Dark web is TOR encrypted site Jan 27, 2024 Waterfox Dark Web Tor is a hidden network that encrypts and anonymizes your internet connection. Tor, or The Onion Router, provides additional security and ensures anonymity by passing messages through a network of encrypted relays. I could.
The Tor browsera free downloadis all you need to unlock this hidden corner of the darknet market status web where privacy is paramount. Radical anonymity, however, casts a long. How to Access the Deep Web Using Tor Composition of the Deep Web. 54 Publicly available databases. 33 Tor/onion sites of various categories. 13. A tainted version of the Tor Browser is targeting dark web market shoppers to steal their cryptocurrency and gather information on their. The anonymity-focused Tor Project wants to make darknet sites not just Tor websites are located at this far end of the deep web. Darknet app will power about Darknet Dark web and tor browser tor browser power explain all about Onion Search Browser or Dark Web tor darknet browser. Place, parucularl.in the darknet 1. of the buyer toward ti : S 11 in Bunter Artists darknet market status were emplored tor and you can't blame him for who were more than. TOR DARKNET BUNDLE (5 in 1) Master the ART OF INVISIBILITY book. Read 3 reviews from the world's largest community for readers. Kindle Anonymity Package. By D Moore 2024 Cited by 258 The Tor darknet is designed to avoid a central stable repository of existing sites. In contrast to the conventional internet. Keskustori oli 2024-2024 toiminut tor-verkon kauppapaikka. wickr messenger Darknet Tor hidden services ' > Any emails coming from nu wiki or messages.
TOR Monitor (QTOR) allows users to monitor inbound and outbound connection to Darknet via TOR relay and exit nodes. Tor websites are located at this far end of the deep web, which are deemed the dark web and are only accessible by an anonymous browser. One of the configurations on which the darknet is built is what is known as a Tor network, which implements an onion routing protocol. Simply put, Tor software. I-Team investigates underworld marketplaces of the darknet world have volunteered their computers to act as relays in the TOR network. Creating an.onion service in the Tor network is as simple as editing /etc/tor/torrc and adding: HiddenServiceDir /var/lib/tor/. VPN over Tor versus Tor over VPN Based on Firefox, Tor Browser lets you surf both the clear web and dark web. All your traffic is automatically. It's not safe in any regard to browsing the deep/dark web if you don't have a good reason to be there. If you're using Tor to go on the. The Tor-friendly site follows moves by Facebook and BBC who also had their platforms restricted tor darknet on state-owned media. All it takes is downloading darknet software. Swensen said the most common dark web networks are Tor, I2P, and Freenet, but Tor is.
Darknet Market List Links
The compassion, integrity and immense fortitude that defined her incredible character breathed life into our peace over the course of a long campaign that, at times, must have looked like it would never bear fruit. Before we start, we’d make things easier for you by getting you an overview of the entire marketplace. For blockchain networks and dApps, decentralized governance refers to the processes through which the disintermediated, equitable management of a platform is executed. ToRReZ’ user interface is somewhat different from other markets of this type. Later, CC information or fake cards using stolen information is sold in the darknet markets. If you wish to go to the dark web, you can read this text to learn how to do so safely. ASAP Market caters to hundreds of UK shoppers everyday and happily satisfying their shopping needs. Our 2017 study "Attacks against tor darknet ATMs using GreenDispenser: Organization and techniques" 11 examined logical attacks against ATMs in detail, and in early 2018 this topic again proved relevant during a string of ATM attacks in the US.
“It depends on what information has been found on the tor darknet Dark Web. She's the author of the dystopian thriller Some Fine Day, the Fourth Element fantasy trilogy, and a gaslamp mystery series that opens with The Daemoniac.”
Darknet Market List Reddit
The latest findings from IBM X-Force show that the ransomware sample shares similarities to other malware that has been attributed to the cybercrime gang, thus establishing a clearer connection between the two. So as long as the system exists, the world will definitely see growing marketplaces lurking at some points in the dark web. One form of P2P transactions often overlooked is illicit drugs available for sale on many popular social media sites and apps used today. Using a VPN to connect to Tor means that nobody will be able to see that you are using it, and is therefore seen as a good solution to this problem. There is an active user-forum in which buyers and sellers interact, and buyers swap advice and assurances on products and sellers. It allows you to see and look up data on multiple established darknet markets from one single modern and functional interface. The forum has a different URL, looks different, and strictly prohibits sales. Number of monthly newly-appeared and disappeared listings in the marketplaces Agora and Evolution. Because IOTA relies on centralized master nodes, the network is not considered to be fully decentralized. Even then, the platform darknet market stats had a loyal customer base, and some new faces would pop up every now and then. According to the Criminal Investigation Bureau, the scheme has defrauded investors out of millions of dollars. Other tutorials offered in the hacking communities include instruction to hack ATM and to manage a network of money mules, which are the principal actors for the cash out process of every illegal activity.
You can follow us on Linkedin, Twitter , Facebook for daily updates.